Before we start to dive into standards, policies, procedures, training and many cyber security controls, let us first look at an example of an incident we will be facing; Ransomware.
Ransomware Incident
To put it simply a ransomware incident is a situation where a company finds itself being blackmailed to pay an amount (a ransom) in cryptocurrency, mostly bitcoin to a criminal group that has exfiltrated data from the organization's network environment, encrypted all the files within the network, inhibited ways in which data can be restored from backups and is now threatening to expose the exfiltrated data in the darkweb unless the ransom amount is paid.
Below we will demonstrate how a ransomware incident looks like.
To understand the entire experience of a ransomware event, I would recommend reading these Documents
- ‘Your Data is Stolen and Encrypted’: The Ransomware Victim Experience by Royal United Services Institute for Defence and Security Studies RUSI.
- Conti Cyber Attack on HSE Independent Post Incident Review
Install Tor Browser
I am going to take you to the dark web to see first hand how this data is exposed on the internet and how much ransom amounts the criminal gangs as for. To do this you need a special browser known as Tor. Download and Install this according to your operating system of choice. The manual for installing Tor will not be included in this article.
Ransomware.live
Once you have finished installing Tor, open it and open the link Ransomware.live.
This website provides an updated list of companies worldwide that have been listed in Data Leak Sites belonging to the different Cyber Criminals. Quite a number of these links are Dark web links, therefore be very careful when downloading these files and running them in your machine.
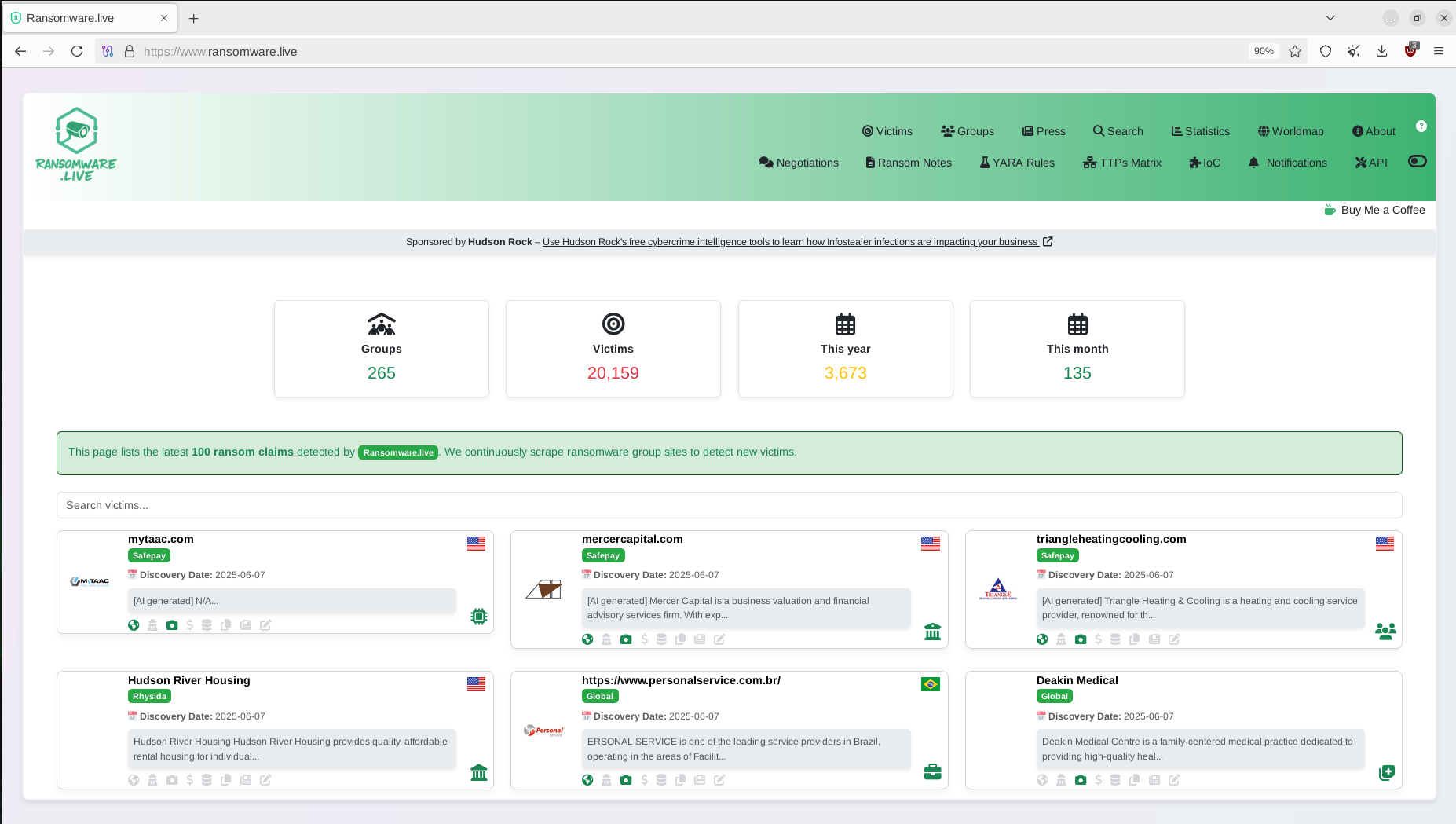
There are very many sites of s similar nature on the internet.
Threat Actor
Since I have been hired by an Institution in the HealthCare Industry as well as Education industry, I will be looking at Rhysida Ransomware group as one of the threat actors these organizations will be facing as as I am building a Cyber Security Strategy. Rhysida ransomware group targets organizations in the following Industries
- Healthcare
- Education
- Government
- Manufacturing
- Information Technology
We will therefore search for the Rhysida Ransomware group.
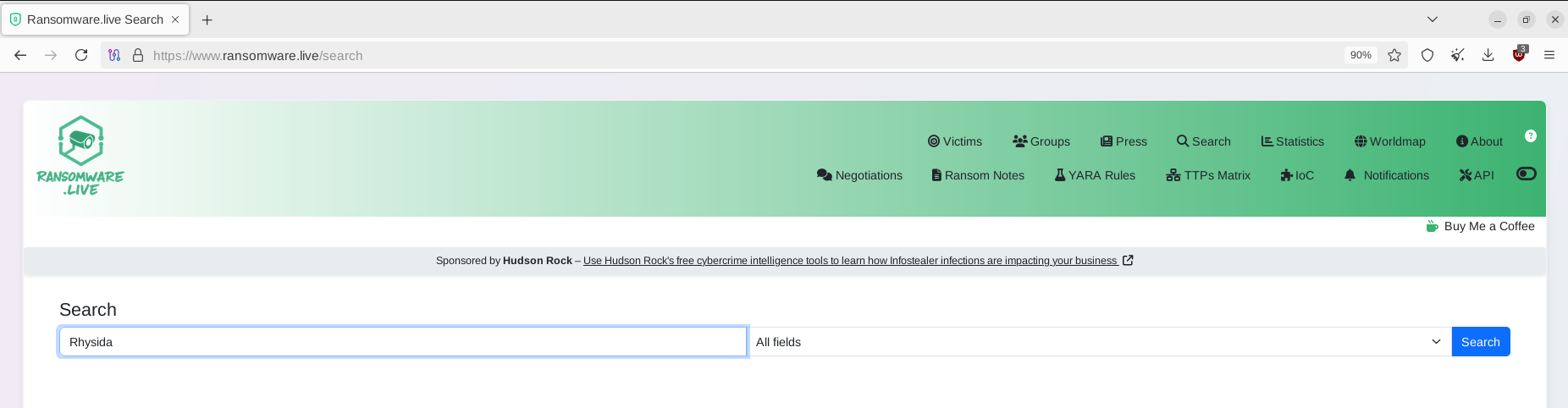
In the results we will scroll down until you find Matching groups
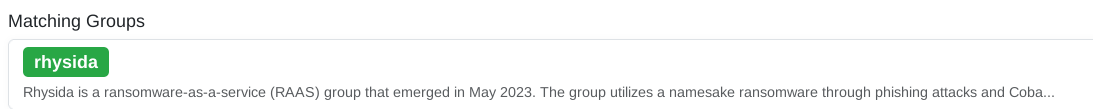
The Rhysida profile page will come up. Scroll down until you find locations and click on the arrow to reveal the darkweb links. Click on any of them and try to open the Rhysida Ransomware Data Leak Site.
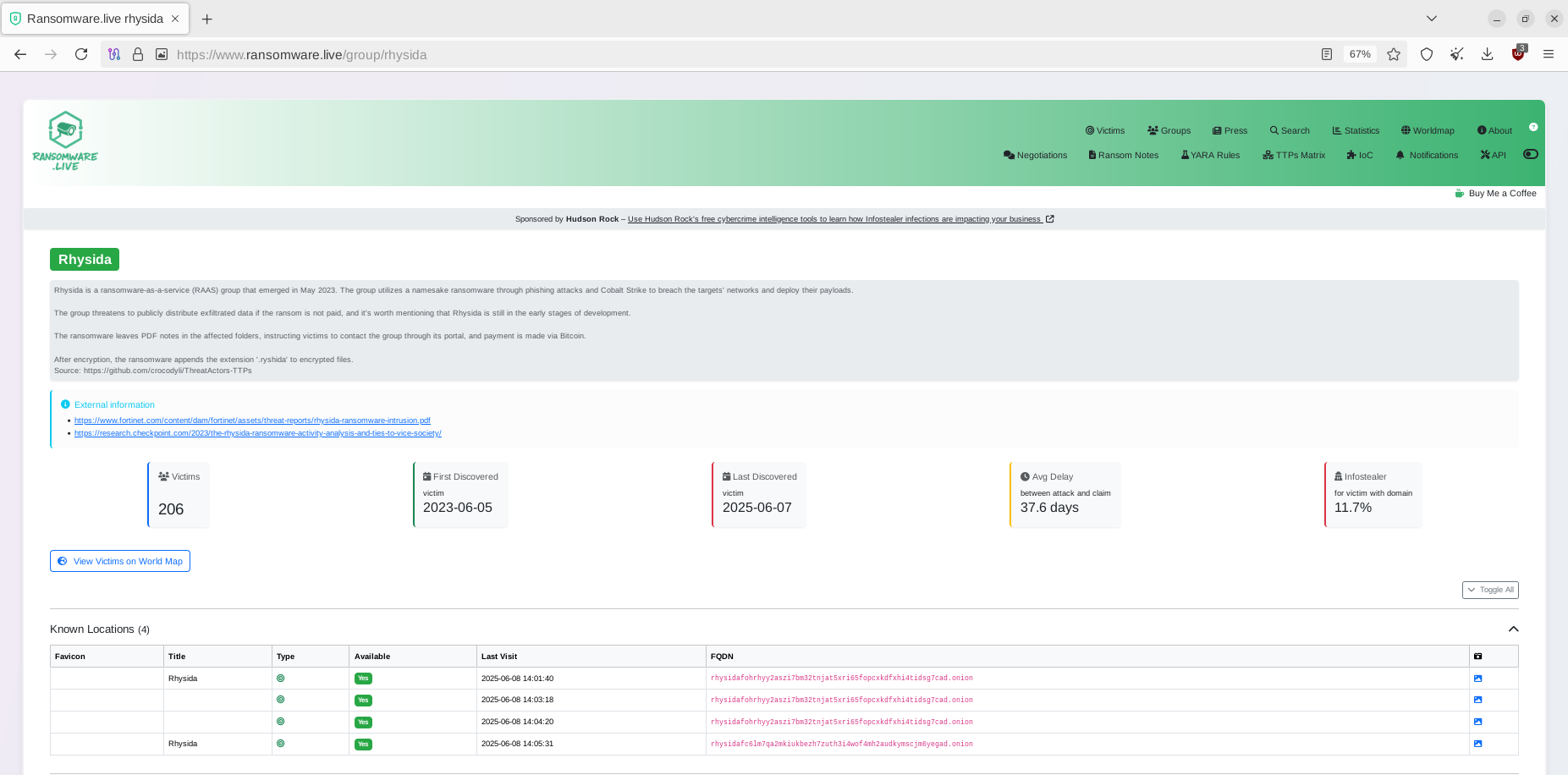
This is the landing page which shows the logo, total number of victims that have been listed. Number of new victims that are in the progress of being extorted.
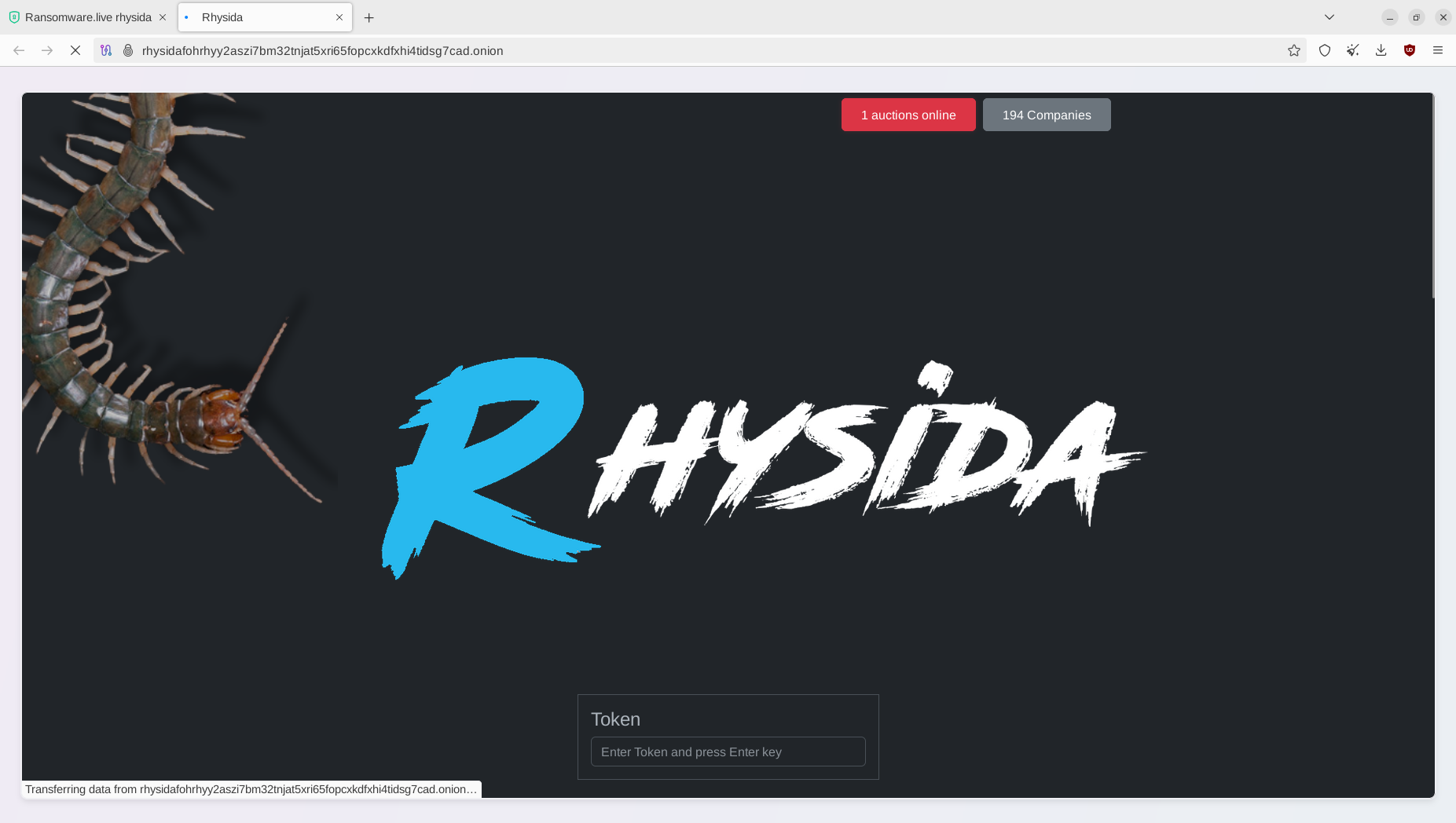
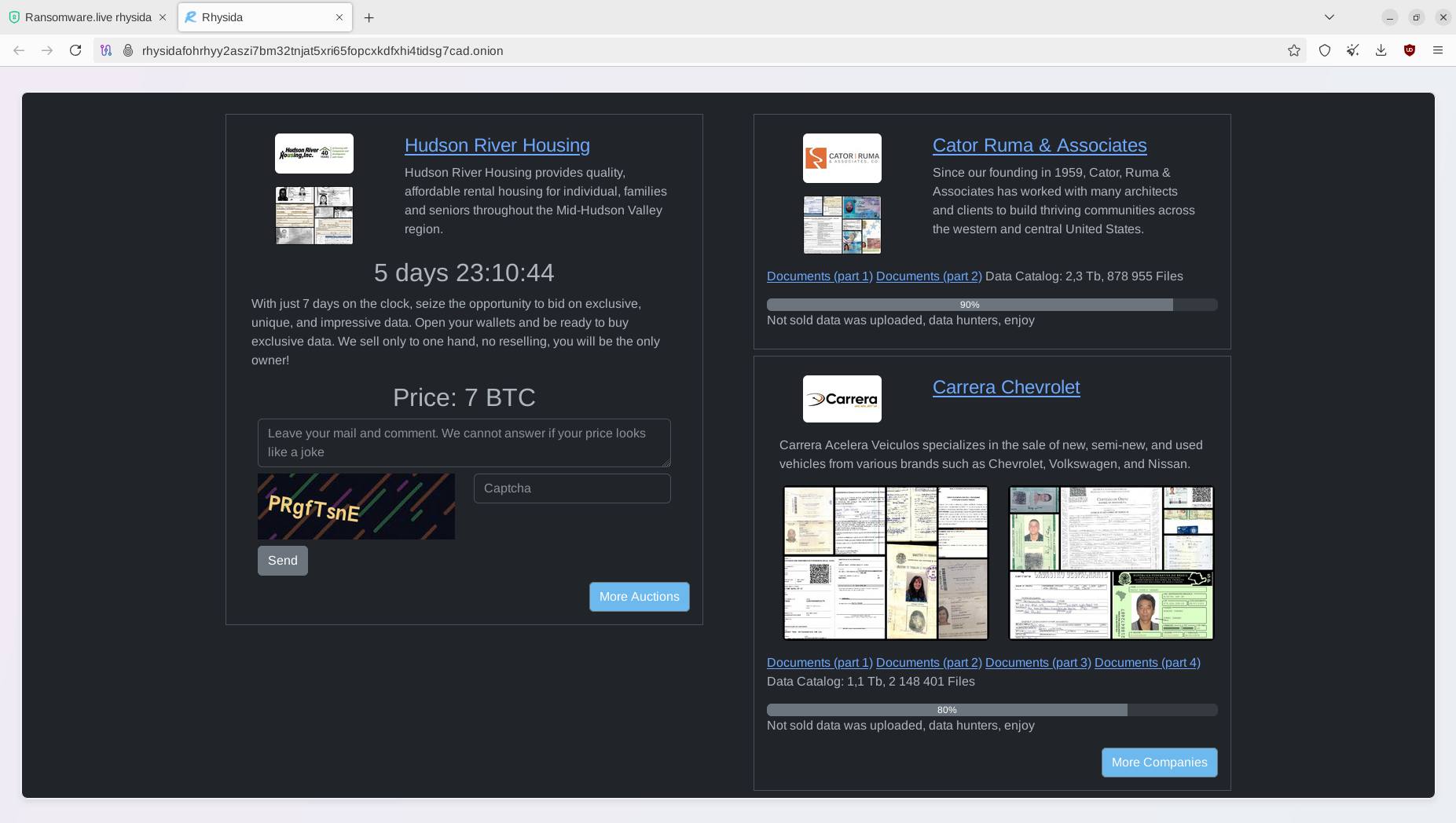
When we scroll down we will see the most recent victims they are extorting, the amount of time the victim has until full data disclosure and the ransom amount.
Ransomware Incident - What actually happens
We will select one of Rhysida's ransomware victims, Abdali Hospital. This ransomware event occured in 26th of December 2023. Abdali Hospital is located in Jordan and is a 200-bed multi-specialty hospital with the mission to provide best practice patient-centred care and promote research and education.
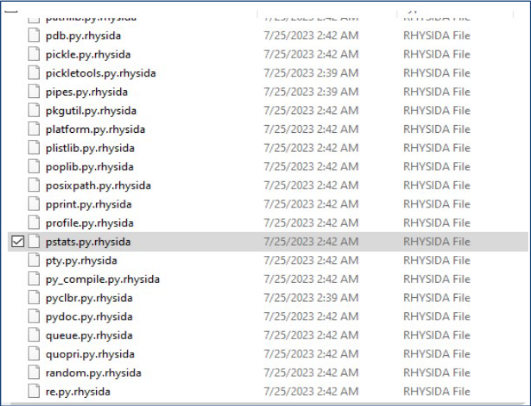
Rhysida gained access to the Abdali Hospital Network and encrypted all the files within the hospital. I will describe how they perform this process in the next article. The image below shows an image of how the files will looked like within the entire network after the Rhysida's encryption software has been run.
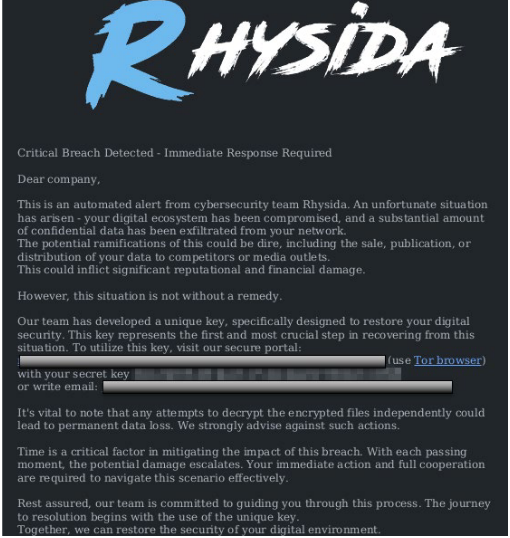
Once the files have been encrypted, a ransom note is left on the machines telling the organization how to communicate with Rhysida
A timer timer is placed by Rhysida Ransomware group of which when the time elapses, the data will be released. This is a tactic to add more pressure to the management of the organization to pay the ransom. Also released is partial data that Rhysida acquired from the Abdali network
The following is an illustration of what is happening within Abdali hospital during the ransomware event
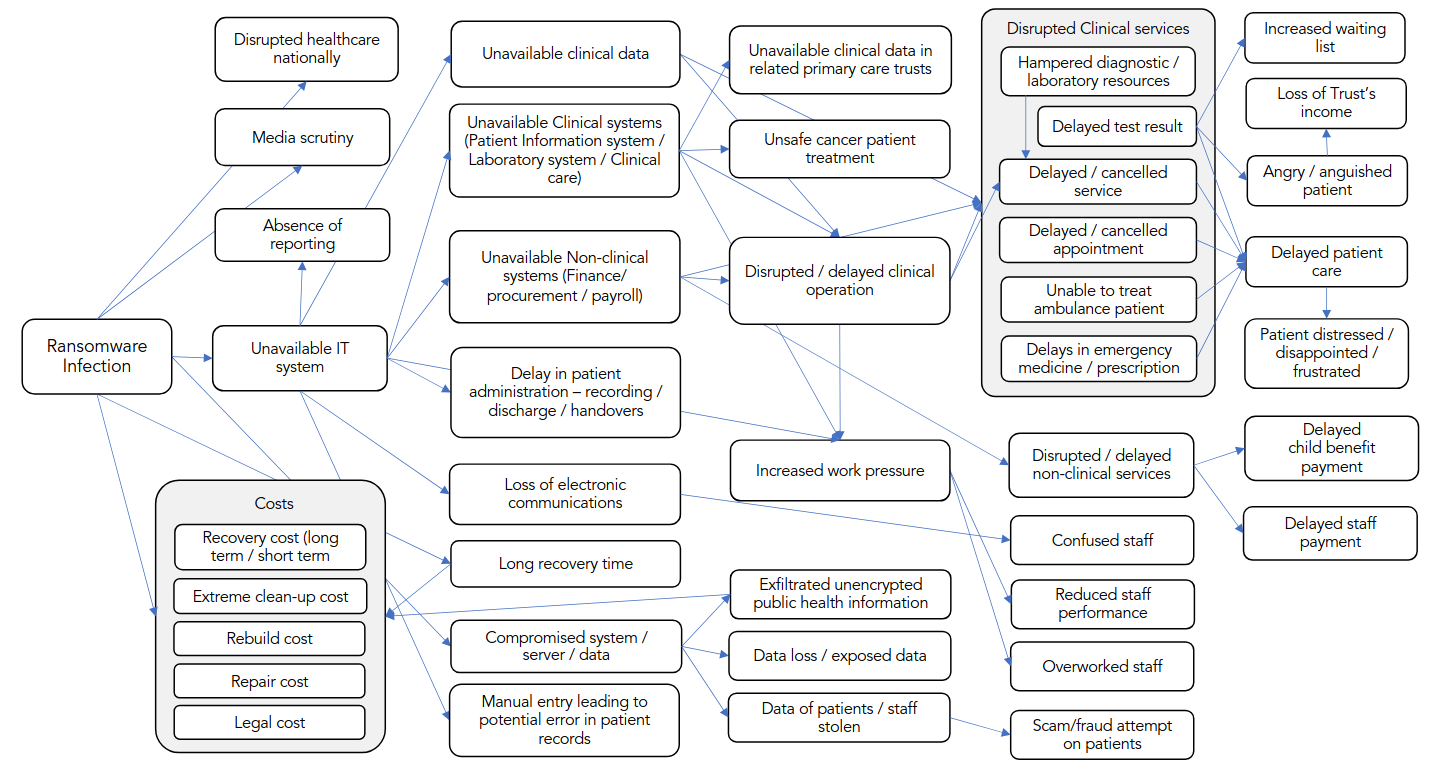
The situation above varies depending on the organization that has fallen victim to a ransomware. Try and draw out what will happen in your organization when you lose all computer systems to ransomware.
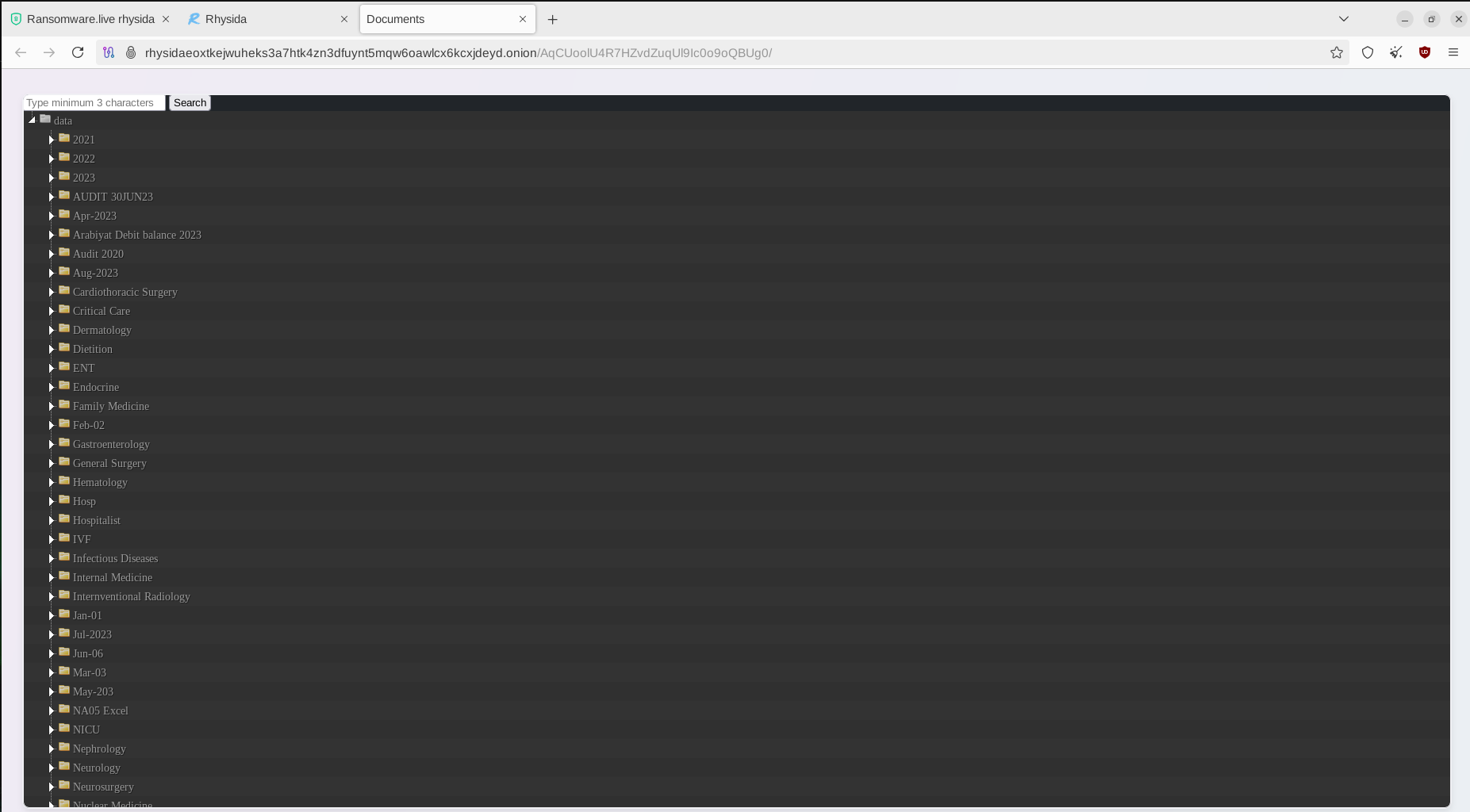
Once the timer runs out, and the ransom amount has not been paid, the data is released as was in the case of Abdali Hospital, 100% of the data was released. Clicking on the victim page on Rhysida's Data Leak website and select Documents, a new window opens and you can be able to access the victim's files that were exfiltrated, in this case we can see Abdali Hospital Files.
In summary, the picture below really describes what a ransomware incident really looks like, this is the situation that an organization finds itself during a ransomware incident.
This ladies and gentlemen is what we are preparing to prevent and if it happens, we are prepared to take the necessary steps to reduce the impact.
References
- CISA - #StopRansomware: Rhysida Ransomware
- HHS - Rhysida Ransomware
- It’s more than just money: The real-world harms from ransomware attacks
- Royal United Services Institute for Defence and Security Studies RUSI ‘Your Data is Stolen and Encrypted’: The Ransomware Victim Experience by .
- Independent Post Incident Review - Conti Cyber Attack on HSE
