Now that we have seen what an Incident looks like, the question becomes, what approach should we take to prevent such an Incident from happening in your organization?
The Pyramid of Pain
"If you know yourself but not the enemy, for every victory gained you will also suffer a defeat.." Sun Tzu
Think of Cyber Security as a boxing match, it is us (The defenders) the blue side In one corner Vs the Ransomware gangs the Red Side on the other corner.
In order to be able to defend properly, It is important for you to know your enemy. You need to understand how these gangs are coming at you, what methods are they using, what tools are they using, what are their steps and procedures and if possible know and understand how they train.
The point is simple, We want to make their attack against us as difficult as possible, slow them down as much as possible.
There are so many controls we that we can apply, the main question is, if you are new to this, where would you start?
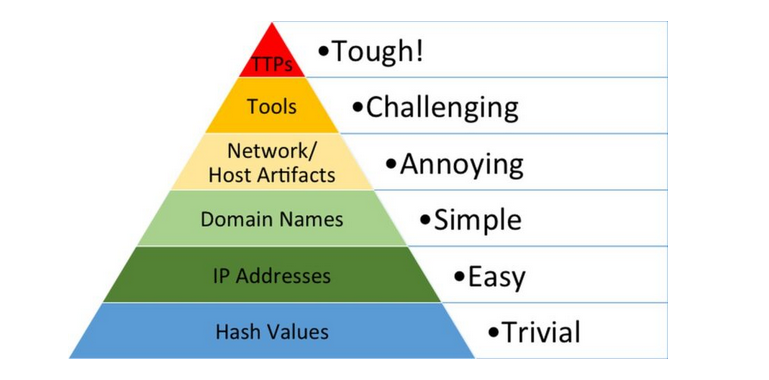
The Pyramid of Pain is where you start. The pyramid of pain provides you with a list of things that the Attackers use in the process of an attack and how difficult it is for them to change these things. The higher you go up the pyramid, the more challenging it becomes for the attackers to change.
We will therefore jump straight to the top, since we would like to make it as challenging for them as possible, where we have TTPs (Tactics, Techniques and Procedures). These define the steps, methods and tools used by the attacker from the time they start investigating about you to the point where they move (Exfiltrate) data out of your network.
These TTPs are well defined in a framework known as the MITRE ATTA&CK Framework.
This framework will help you Start understanding the enemy - In our case Ransomware gangs - Rhysida
MITRE ATT&CK Framework
The MITRE ATT&CK Framework is an encyclopedia that consists of known threat actors, the tactics, techniques and tools (software) they use to achieve their objectives.
- Tactics These represent the steps taken by the adversaries during the process of the attack. These are goals along the process of the attack.
- Techniques Represents the particular way(s) that a threat actor has accomplished a step during the process of the attack.
- Procedures these show real world examples of the malware/tools/software/commands that the threat actors used to achieve a technique
This framework forms the foundation of Cyber Security Language and other Cyber Frameworks. The MITRE ATT&CK Framework consist of various tools that provide Cyber Professionals a number of services. To understand more about this framework, complete the exercise on MITRE on the TryHackMe Platform.
There are MITRE ATT&CK Frameworks available, Enterprise (OnPrem) Network, Industrial Control Systems (ICS), Mobile Devices and Cloud
Look at it this way, an attack towards an organization is like a manufacturing process, there are a number of steps attackers must use to achieve their objective. In addition, each step has unique tools/software that are used.
In order for us to defend well, we must understand this process, the steps taken and the tools used in each step.
We will first begin with understanding the Tactics for Enterprise MITRE ATT&CK
- Reconnaissance This is how threat actors find out information about your organization before they attack. They can look for information that is published or exposed on the internet or they can acquire information by directly interacting with people or equipment belonging the organization
- Resource Development This is where the adversary collects all the necessary resources they require in order to carry out a successful attack. These can vary from the malware used, the infrastructure (command and control servers) to use, access credentials that will work within the organization.
- Initial Access These describe the various ways an attacker can use to get a foothold in the victim network
- Execution This describe how the threat actor will run malicious code within the victim network and machines
- Persistence These are the methods that attackers use to maintain access to systems across system reboots, change of login credentials and other interruptions that could interfere with their access.
- Privilege Escalation Most of the time when adversaries acquire initial access to a network, they have low level user access. Privilege Escalation lists the methods the attackers will use to gain a higher access privileges/permissions on the machines they have accessed and consequently the network in order to access higher value targets.
- Defense Evasion These are the methods they use to bypass the security measures that have been put in place for example bypass antivirus and End Point Detection mechanisms that have been installed
- Credential Access This describe the methods through which the attackers acquire legitimate log in credentials, valid usernames and passwords, as they traverse through the victim network. Using legitimate access credentials makes it way much harder to detect
- Discovery
- Lateral Movement Once the threat actor gets access to a corporate network, they would want to move from one computer to the next until they reach their objective, crown jewels.
- Collection
- Command and Control hacking a network is quite a tedious undertaking and once he threat actors have gained initial access, the first thing they will want to do is to maintain perpetual access to the network. Command and Control is how they are able to maintain communication access between themselves and the devices in corporate network they are have already compromised. Command and Control also provides ways to run commands within the network and means to exfiltrate data
- Exfiltration This lists the methods used to move data from the Corporate network to storage and computers that the threat actors control.
- Impact Describes the various ways the victim organization can be affected by a cyber attack.

Rhysida's TTPs
We can get well documented Rhysida TTPs from a number of reputable companies, for our case we will use the TTPs that have been defined by by CISA Alert/Advisory on #StopRansomware: Rhysida Ransomware.
First and foremost, let me give you a tip, This document is the one!
One of the core pillars of Cyber Security is this document. If you understand what is happening in this Document, you are halfway there, really.
Please note the language used comes from the MITRE ATT&CK Framework
Below is a summary of Rhysida's TTPs
- Resource Development
- Develop Capabilities - Develop Malware Rhysida-0.1
- Initial Access
- Valid Accounts - Internal VPN Accounts
- Execution
- Command and Scripting Interpreter: Cloud API AZCopy to Azure
- Command and Scripting Interpreter - PowerShell
- Command and Scripting Interpreter: Windows Command Shell
- Privilege Escalation
- Process Injection:Portable Executable Injection
- Defense Evasion
- Indicator Removal - Clear Windows Event Logs using
wevtutil.exe - Indicator Removal - File Deletion Powershell Commands to delete binary strings
- Hidden Artifacts - Hidden Powershell Windows
- Indicator Removal - Clear Windows Event Logs using
- Credential Access
- OS Credential Dumping - NTDS
- Modify Registry
- Discovery
- System Network Configuration Discovery -
ipconfig - Remote System Discovery -
“domain computers” /domain - System Owner/User Discovery -
whomai&net - Permission Groups Discovery: Local Groups -
net localgroup administrators - Permission Groups Discovery: Domain Groups -
“domain admins” /domain - Account Discovery: Domain Account -
[username] /domain - Domain Trust Discovery
nltest
- System Network Configuration Discovery -
- Lateral Movement
- Remote Services - Remote Desktop Protocol
- Remote Services - SSH
- Collection
- Remote Access Software - AnyDesk
- Command and Control
- Remote Access Software - AnyDesk
- Impact
- Data Encrypted for Impact
- Financial Theft/Extortion
This is how Rhysida fights. We have been provided with the software and commands they use. Now that you understand this, you can start implementing security measures that are directed towards making it difficult for them to perform these actions and if they do you can be able to detect them. This Rhysida alert document by CISA also provides mitigation measures that can be taken to prevent attacks from this particular ransomware group.
References
- CISA - #StopRansomware: Rhysida
- MITRE ATT&CK Framework
- AttackIQ - What is the pyramid of Pain
Assignments
- Tryhackme
